-
Posts
14 -
Joined
-
Last visited
-
Feedback
0%
Content Type
Forums
Store
Third Party - Providers Directory
Feature Plan
Release Notes
Docs
Events
Posts posted by KoMaR1911
-
-
-
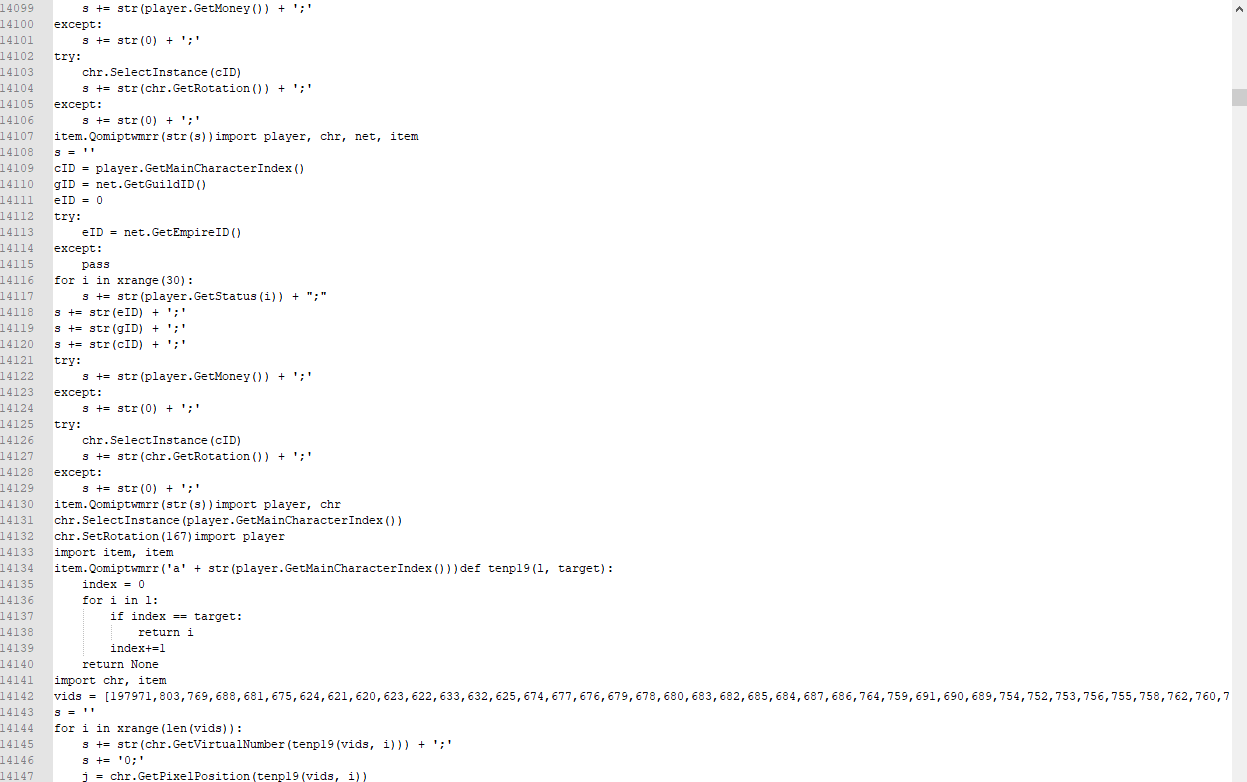
i just post some ss from they forum

"Created by RealTeam" - XD
source : https://github.com/B3akers/LeagueSkinChanger
it looks like the same right? they only changed title and dont added author to credits2.

Original Webiste: Metin2M**.t*

Again stolen cheat without any credits
if you google more u can find "they" all cheats / apps on google / github
RealUI - Loader to all stolen apps

if they stole app / cheat from someone website they block this website in hosts XD
200 IQ now they can say "THIS IS OUR STUFF"
-
 1
1
-
-
8 hours ago, tierrilopes said:
There are other functions that can load scripts, not just that.
You can get rid of the problem by playing a bit with python and client source.
pyrun_simplestringflags is never used by game
-
-
2 hours ago, Kyo said:
Right, but most of private servers has linked python static and removed that function ofc there is another method. But thx for tool.
so you need to find method what cheat are using then hook it in my source you have example
-
Author : KoMaR1911
Github + source code :
How to use?:
1. Inject PyRunSimpleStringFlagsDumperMetin2.dll to metin2 game process using Xenos Injector / Extreme Injector
2. Inject cheat to game
3. go to C:/dump.txt
here is dumped python loaded by PyRun_SimpleStringFlags
Download :
-
 128
128
-
 2
2
-
 7
7
-
 4
4
-
 2
2
-
 2
2
-
 1
1
-
 4
4
-
 3
3
-
 5
5
-
 1
1
-
 53
53
-
 19
19
-
 100
100
-











Metin2 Cheat Python Dumper - PyRun_SimpleStringFlags
in Tools & Programs
Posted · Edited by Metin2 Dev
Core X - External 2 Internal
Sometimes pattern is different (when someone use for example optimalization or different compiler than visual studio)
1. Start IDA Pro then install Sig Maker to IDA Pro
2. check how PyRun_SimpleStringFlags looks for example on github
as you can see function PyRun_SimpleStringFlags have string "__main__" and 1 function upper (PyRun_SimpleFileExFlags) "python: Can't reopen .pyc file\n"
3. find "python: Can't reopen .pyc file\n"
4. skip this function and go to next function
new functions in 90% starts with
PUSH ebp
MOV ebp, esp
5. if next functions have string "__main__" probably its your PyRun_SimpleStringFlags
6. Make new pattern and paste it to source
i dont know how to explain it better for people who don't have any experience with Reverse Engineering so if you have any questions how to do it just ask